Hello everyone,
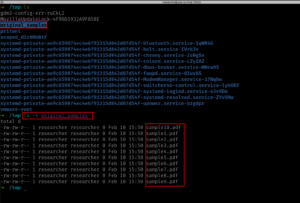
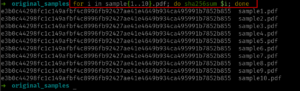
I am logging here the second day of my 30 days challange. Today, I was not able to read much from the book however, I am happy to share with you all a bash tool which can automate you to check whether it is suspicious or not based on the virustotal engine. By the way, you might experience the slowness of the tool, it is because of the rate limit set by the VirusTotal for the freemium user. I have mentioned briefly above it at [here](https://tcert.net/30-days-challenge-day-01/).
In order to use this tool, you will have to have the hashes ready and it should be having **hashes.txt**. The steps were mentioned [here](https://tcert.net/30-days-challenge-day-01/)
I have the tool uploaded here. I am sure it will get updated with passage of time.
“`
#!/usr/bin/env bash
# you have to create virustotal account and get the free API key from there. I have redacted mine.
VT_API_KEY=”redacted”
# Check if API key is set
if [[ -z “$VT_API_KEY” ]]; then
echo “Error: VirusTotal API key is missing. Set it in the script or as an environment variable.”
exit 1
fi
# You have to generate the hashe values of the suspicious PDF files and store the value and name the file as hashes.txt
INPUT_FILE=”hashes.txt”
# Check if file exists
if [[ ! -f “$INPUT_FILE” ]]; then
echo “Error: File ‘$INPUT_FILE’ not found!”
exit 1
fi
# VirusTotal API URL
API_URL=”https://www.virustotal.com/api/v3/files/”
# Read each hash from the file and check with VirusTotal
while read -r hash; do
echo “Checking hash: $hash”
# Send API request
response=$(curl -s -X GET “${API_URL}${hash}” \
-H “x-apikey: ${VT_API_KEY}”)
# Extract the detection status
detected=$(echo “$response” | jq -r ‘.data.attributes.last_analysis_stats.malicious’)
if [[ “$detected” -gt 0 ]]; then
echo “⚠️ Detected by $detected antivirus engines”
# Extract antivirus engines that flagged the file
echo “Detected by:”
echo “$response” | jq -r ‘.data.attributes.last_analysis_results | to_entries[] | select(.value.category == “malicious”) | “\(.key)”‘
else
echo “✅ No threats detected”
fi
echo “—————————–”
# Avoid hitting API rate limits
sleep 15
done < "$INPUT_FILE" ``` Github link: https://github.com/samduk/toolz/blob/main/pdf_to_vt.sh