Today is 22nd March and we are having all India curfew to “stay at Home” from the COVID-19. Had a good breakfast and by the time I was washing my face, a kettle of water is already boiled. So, everything set to pwn the machine.
*********************************************************************************************
Description og the Game:
This VM tells us that there are a couple of lovers namely Alice and Bob, where the couple was originally very romantic, but since Alice worked at a private company, “Ceban Corp“, something has changed from Alice’s attitude towards Bob like something is “hidden”, And Bob asks for your help to get what Alice is hiding and get full access to the company!
Difficulty Level: Beginner
Notes: there are 2 flag files
Learning: Web Application | Simple Privilege Escalation
Download the Machine from this link: Click Here
********************************************************************************************************************************************
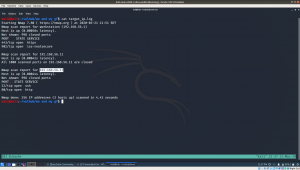
Step 01:
sudo ifconfig
My Kali Linux Machine IP address is: 192.168.56.11
Step 02:
nmap 192.168.56.11/24 > target_ip.log cat target_ip.log
I know save this output because I get confused with different IP addresses (recently I been playing with couple of machines)
So the Target Machine IP address is: 192.168.56.17
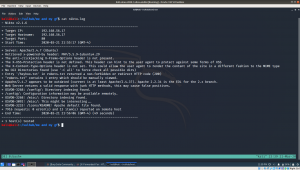
Step 03:
Let’s find what services, service version and port numbers is currently running on it.
nmap -sC -sV -p- 192.168.56.17 -oN nmap.log
It is confirmed that a webserver (Apache) is running on it. Besides, result of step 03 is very important. If we can’t find anything useful, we will have to go through it again and attack another services etc.. So keep this in mind.
Let’s find files in the webserver.. Which usually you can do with nikto or gobuster. I do both.
nikto -h 192.168.56.17 > nikto.log
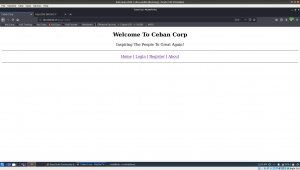
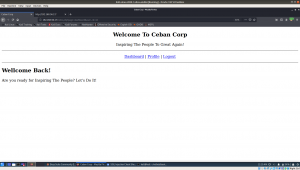
Visit the website and files we found through nikto scanner
1.1 Visit website.
“The site can only be accessed local” which is very important hint. (localhost or 127.0.0.1)
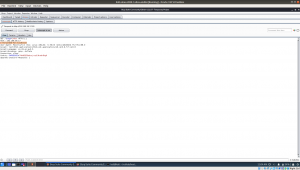
1.2. Source code: Ctrl+U (on firefox)
very important hint “use x-forwarded-for”
To be honest, I know it will act as redirection but I don’t know the syntax so I googled and I got this ..
So the syntax is
x-forwarded-for localhost
1.3 At this time, I just fire-up my burp suite and modified the request. (let me know if you don’t know how to use burpsuite or configure it, in the comment).
I had to manually put the custom header value there on each request (x-forward-for: localhost) However, I am very happy with the result and perhaps when time permits me today, I will read more on how to automate this, so that I won’t have to spend that much time for such task 🙂
Yes, when I see the login page I felt very excited and google few sql cheat sheet right away and start experimenting. Nevertheless, I was no luck. However, if you have read the last couple of post, I did LFI to one of the box. So, I thought why not I open an account and upload my shell in there. (usually this is done during the bug bounty too)
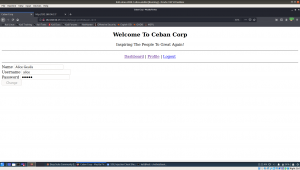
So I began to messing with the ID values up in the URL location. I place 1 there and checked, then 2, and then 3… I enumerate till 6 and I got all the user registered on this website with their password.
If you do remember the game description which is at the very beginning of this write up, our person of the interest is alice.
Yeah, we got the password of user alice.
username: alice password: 4lic3
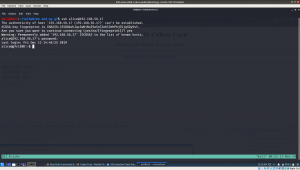
As per the nmap result, we know that the SSH protocol is running on the box.
ssh alice@192.168.56.14
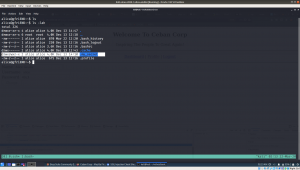
Usually, I used to think how come those blogger knows everything about the box.. Now I realized it. I tried SUID binaries and tried and ran into my rabbit holes, but I didn’t write it here lol
While I was solving the previous box, the author trolled me to wait for password (although there isn’t one) and the user itself is sudo user so no complex exploit is required to root that. Therefore, in this box, I would like to test whether the current user has sudo on it. So I googled the syntax and guess what I got?
Yes, /usr/bin/php has root privilege enabled on it.
I know through python, we can escalate the privilege by writing three lines of code (to set value for setuid, setgid). However, I have no idea with PHP. So I googled a little and thought it will be faster to ask some pointer from OSCP STUDY GROUP.
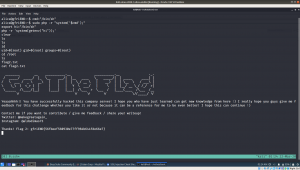
Indeed I got help and I was able to root it within few seconds. (using this link)
So I will not write details of it, because everything is there in that link. Probably you should read a little too 🙂
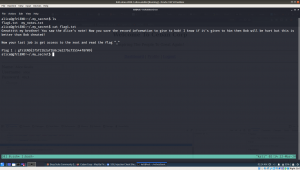
As per the requirement, we need to get two flags and root the system.
So far we root the system and got one flag.
However, another one I am not sure where it is. Let’s use the power of find command lol
find / -name gfriEND*
No, I didn’t find anything. Let’s enumerate again carefully this time…
Yes, indeed.. it is here… fishhhhhhh lol
Final Assign and message which Bob wish to know is here.
Going to prepare lunch now.. Hopefully I could take down another box today 🙂